Virtual Private Network (VPN):
Virtual Private Network (VPN): Encrypted internet connection that provides a secure, private network connection for…
Virtual Private Network (VPN): Encrypted internet connection that provides a secure, private network connection for safe data transmission.
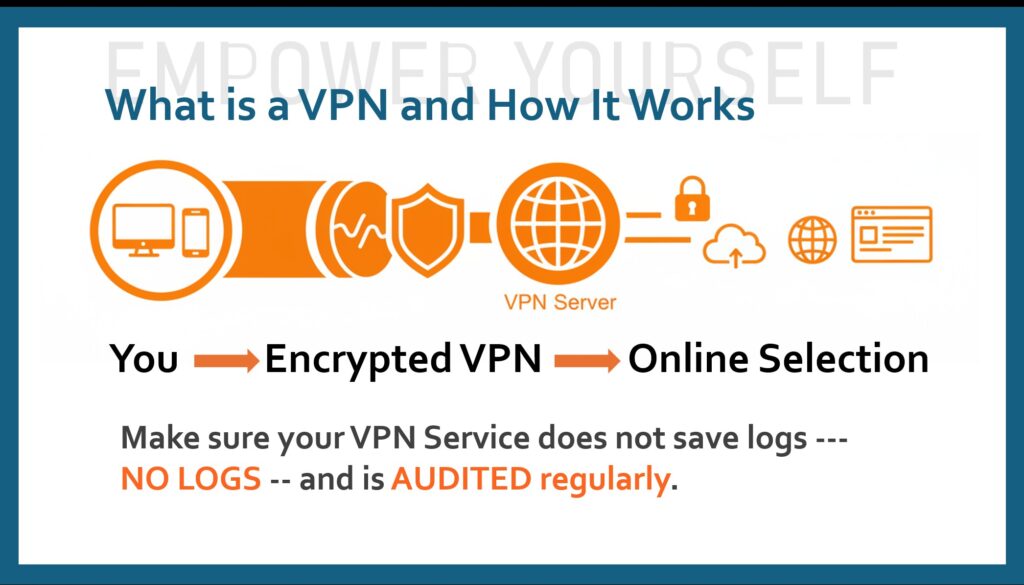
A Virtual Private Network (VPN) works by creating a secure, encrypted “tunnel” between your device and a remote server operated by a VPN provider. This process shifts your internet connection from your local Internet Service Provider (ISP) to the VPN’s private server, masking your identity and securing your data.
How the Connection Works
The transition from an open connection to a protected one happens in several steps:
- Authentication: When you launch the VPN app and click “connect,” the client software on your device verifies your identity with the VPN server.
- Encryption: All outgoing data from your device is “scrambled” into unreadable code (ciphertext) using a secret key known only to your device and the VPN server.
- Tunneling: The encrypted data is encapsulated—wrapped inside another data packet—and sent through a secure “tunnel” across the public internet.
- Decryption: Once the data reaches the VPN server, it is unwrapped and decrypted back into its original form.
- Forwarding & Masking: The VPN server sends your request to the intended website. Because the request originates from the server, the website sees the VPN’s IP address and location instead of your own.
What a VPN Hides
By routing your traffic through this encrypted tunnel, a VPN effectively conceals:
- Your IP Address: Your digital “home address” is swapped for the server’s, hiding your physical location.
- Browsing Activity: Your ISP can see that you are connected to a VPN, but they cannot see which specific websites you visit or what data you send.
- Data Content: Sensitive information like passwords, credit card numbers, and private messages are encrypted and protected from hackers, especially on public Wi-Fi.
When looking for a VPN service, make sure they do not save LOGS and they are audited regularly.